Crimson Desert Hypervisor Bypass: The upcoming open-world action RPG Crimson Desert has quickly become one of the most anticipated games among PC and console players. Developed by Pearl Abyss, the studio behind Black Desert Online, the game promises cinematic combat, a massive open world, and a deep story.
However, alongside the excitement, another term has started trending in the PC gaming community: Crimson Desert Hypervisor Bypass.
Many gamers searching this term want to understand what it means, how it works, and why it is being discussed across forums and YouTube videos.
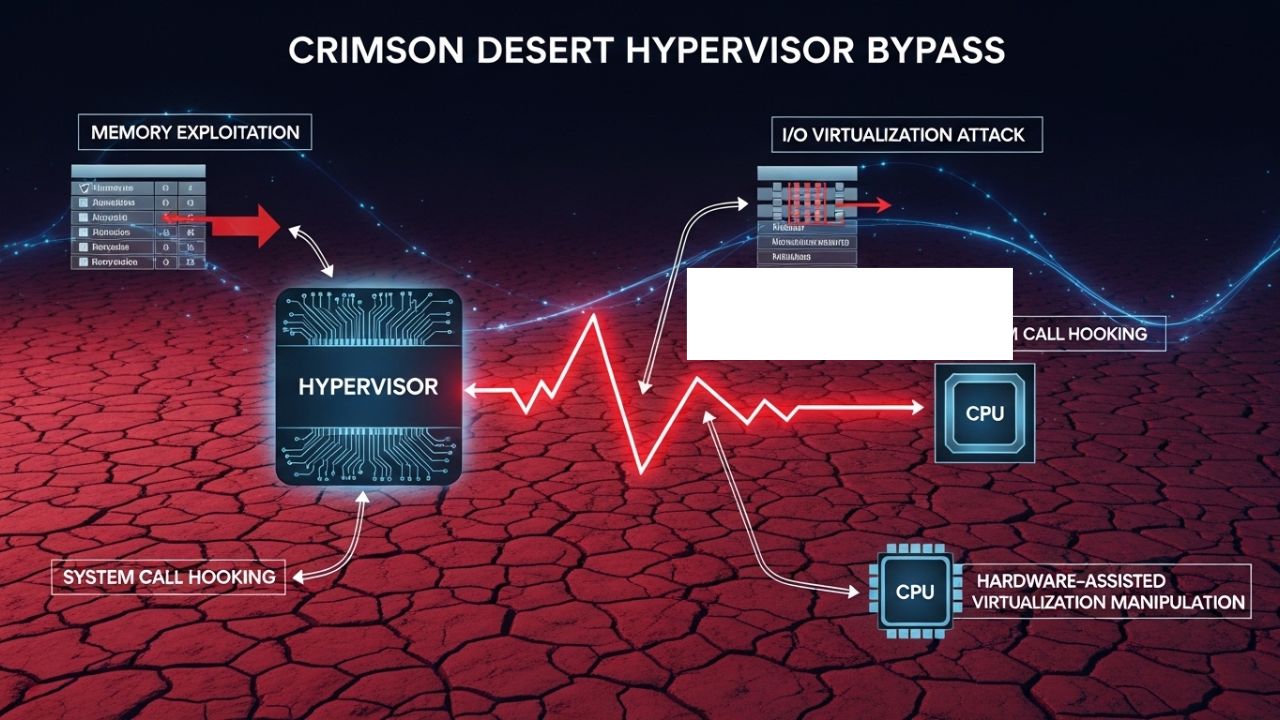
In simple terms, the Crimson Desert hypervisor bypass refers to a method that uses system-level virtualization to interfere with anti-tamper protections used in modern PC games. In this guide, we’ll explain the concept, the technical idea behind it, and what PC gamers should know before experimenting with such methods.
Crimson Desert Hypervisor Bypass: Overview
| Detail | Information |
|---|---|
| Game | Crimson Desert |
| Developer | Pearl Abyss |
| Publisher | Pearl Abyss |
| Release Window | Expected 2025 |
| Platforms | PC, PlayStation, Xbox |
| Genre | Open World Action RPG |
| Engine | Pearl Abyss Proprietary Engine |
| Key Features | Cinematic combat, open world exploration, story driven gameplay |
What is Crimson Desert Hypervisor Bypass?
The Crimson Desert Hypervisor Bypass is a technical method discussed in the PC gaming community that attempts to bypass anti-tamper systems used in some games.
Modern PC games often use advanced protection systems like Denuvo Anti-Tamper to prevent piracy or unauthorized modification.
These protection systems check:
- the operating system
- game memory behavior
- system integrity
- hardware configuration
A hypervisor bypass attempts to run the game inside a controlled virtualized environment where these checks can be manipulated.
Why the Term “Hypervisor”?
A hypervisor is software that runs at a lower level than the operating system and controls virtual machines.
Examples include:
- VMware
- VirtualBox
- Microsoft Hyper‑V
Instead of modifying the game directly, a hypervisor method changes how the game interacts with the system.
How Hypervisor Bypass Works (Simplified)
To understand the idea behind the Crimson Desert hypervisor bypass, we need to understand how modern CPUs work.
Most modern processors support hardware virtualization features such as:
- Intel VT-x
- AMD-V
These technologies allow systems to run virtual machines.
Core Idea
The hypervisor runs at a deeper level than the operating system, sometimes referred to as Ring-1 or Ring–1 in system architecture.
Because of this, it can intercept or manipulate system instructions.
In theory, this allows:
• modifying system calls
• hiding certain processes
• emulating hardware behavior
• bypassing integrity checks
After these changes, the anti-tamper system may believe everything is normal.
However, this method is highly experimental.
Why Gamers Started Talking About It
The topic became popular because some heavily protected PC games take months to crack.
Hypervisor-based techniques gained attention because they claim to work faster.
Reasons the method attracted attention
• It works at a deeper system level
• It may bypass certain anti-tamper checks
• It can theoretically work on multiple games
• It does not modify game files directly
However, popularity does not mean reliability.
Many users report mixed results.
System Requirements for Hypervisor Methods
Community tutorials discussing the Crimson Desert Hypervisor Bypass often mention several requirements.
Common setup requirements
• CPU virtualization enabled in BIOS
• Administrator privileges
• Modified driver permissions
• Windows security settings changes
These steps allow the hypervisor software to load and control system behavior.
Important Warning
Changing these settings can affect system security and stability.
Some configurations may disable important Windows protections.
Risks of Using Hypervisor Bypass
While the idea sounds interesting technically, it also comes with several risks.
Stability Issues
Because hypervisor methods interact with very low-level system functions, problems can occur such as:
• system crashes
• blue screen errors
• game launch failures
• driver conflicts
Even small differences in hardware configuration can cause major issues.
Security Concerns
Many hypervisor tools available online come from unknown sources.
Installing such tools can expose your system to:
- malware
- spyware
- unauthorized system access
This is why security experts advise caution.
Performance Impact
Another question PC gamers often ask is whether the bypass affects performance.
Since hypervisor methods introduce an extra system layer, performance may change.
Possible performance issues
• random frame drops
• longer loading times
• CPU overhead
• unexpected crashes
However, performance varies depending on the system configuration.
Some players report normal gameplay, while others encounter serious stability problems.
Crimson Desert Gameplay Features
While technical discussions about bypass methods exist, the real reason gamers are excited is the gameplay of Crimson Desert itself.
The game combines action combat with cinematic storytelling in a large open world.
Combat System
The combat system in Crimson Desert focuses on realistic physics and cinematic action.
Players can perform:
- combo attacks
- grappling moves
- environmental interactions
- counter attacks
Combat is designed to feel dynamic and heavy, unlike traditional MMO-style combat.
Combat Features
• melee weapon combos
• enemy grappling
• cinematic finishers
• destructible environments
These mechanics create intense battle scenarios.
Open World Exploration
One of the biggest features of Crimson Desert is its huge open world.
Players can explore different environments including:
- mountains
- forests
- villages
- battlefields
Exploration Activities
• hidden quests
• random encounters
• treasure locations
• environmental puzzles
This encourages players to explore the world freely rather than following a strict path.
Story and Characters
The story follows a group of mercenaries navigating political conflict in a harsh fantasy world.
The main character Kliff leads a band of fighters who face war, betrayal, and survival challenges.
The narrative focuses on:
- character relationships
- moral decisions
- large scale battles
This cinematic storytelling style is one of the game’s biggest selling points.
Tips for PC Players Waiting for Crimson Desert
If you plan to play Crimson Desert on PC, here are some useful tips.
Beginner Tips
• keep your graphics drivers updated
• monitor official developer announcements
• avoid downloading unknown system tools
• use legitimate game platforms
These steps help ensure a stable gaming experience.
Expert Opinion
From a gaming industry perspective, the discussion around Crimson Desert Hypervisor Bypass shows how advanced anti-tamper technology has become.
Game developers constantly improve protection systems, while the PC piracy scene continues experimenting with new techniques.
However, the safest and most stable way to enjoy a game like Crimson Desert is through official releases.
This guarantees updates, patches, and full game functionality.
Frequently Asked Questions (FAQs)
What is Crimson Desert Hypervisor Bypass?
It refers to a method discussed in PC gaming communities that uses virtualization technology to interfere with anti-tamper protection systems in order to run the game without standard verification.
Does hypervisor bypass affect performance?
Performance impact varies depending on system configuration. Some users report normal performance, while others experience crashes, stutters, or instability due to system-level changes.
Is hypervisor bypass safe?
Not always. Many tools available online come from unknown sources and may pose security risks or cause system instability.
Why is hypervisor bypass discussed for Crimson Desert?
The topic gained attention because modern PC games often use strong anti-tamper systems, and hypervisor methods are being explored as experimental ways to bypass them.
Do all CPUs support hypervisor methods?
Most modern processors support virtualization features, but compatibility depends on the CPU model, motherboard settings, and operating system configuration.
What is the safest way to play Crimson Desert?
The safest method is to play the official game version from authorized platforms, ensuring proper updates, stability, and online features.
Crimson Desert Combat System: Complete Guide (2026)

Surya Gupta is a professional blogger and SEO specialist with over five years of experience in digital content creation. He writes about technology, smartphones, games, trading, and trending topics. Through his websites, he aims to provide clear, accurate, and helpful information to readers.